3.4 KiB
bootbridge
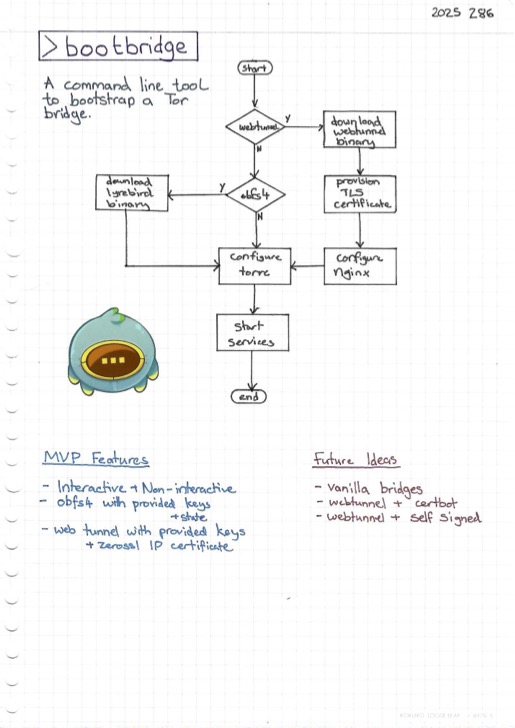
A command line tool to bootstrap a Tor bridge (not to be confused with bridgestrap).
Purpose
You want to run many Tor bridges and would like to quickly bootstrap them from a fresh Debian installation.
Requirements
- Debian stable VM fresh out of the box that won't be used for any other purpose
- Either:
- SSH access to that box
- Ability to give it cloud-init user data
Caveats
- Many cloud providers now implement network firewalls outside the control of the operating system. This is good for security in that if the virtual machine is compromised, it's not possible to change the firewall rules, but it also means that you can't deliberately change the firewall rules from inside the virtual machine. If your cloud has such a feature, it'll be up to you to configure that separately, perhaps with OpenTofu.
Concept
Copyright
Copyright © 2022-2025 SR2 Communications Limited.
Redistribution and use in source and binary forms, with or without modification, are permitted provided that the following conditions are met:
- Redistributions of source code must retain the above copyright notice, this list of conditions and the following disclaimer.
- Redistributions in binary form must reproduce the above copyright notice, this list of conditions and the following disclaimer in the documentation and/or other materials provided with the distribution.
THIS SOFTWARE IS PROVIDED BY THE COPYRIGHT HOLDERS AND CONTRIBUTORS “AS IS” AND ANY EXPRESS OR IMPLIED WARRANTIES, INCLUDING, BUT NOT LIMITED TO, THE IMPLIED WARRANTIES OF MERCHANTABILITY AND FITNESS FOR A PARTICULAR PURPOSE ARE DISCLAIMED. IN NO EVENT SHALL THE COPYRIGHT HOLDER OR CONTRIBUTORS BE LIABLE FOR ANY DIRECT, INDIRECT, INCIDENTAL, SPECIAL, EXEMPLARY, OR CONSEQUENTIAL DAMAGES (INCLUDING, BUT NOT LIMITED TO, PROCUREMENT OF SUBSTITUTE GOODS OR SERVICES; LOSS OF USE, DATA, OR PROFITS; OR BUSINESS INTERRUPTION) HOWEVER CAUSED AND ON ANY THEORY OF LIABILITY, WHETHER IN CONTRACT, STRICT LIABILITY, OR TORT (INCLUDING NEGLIGENCE OR OTHERWISE) ARISING IN ANY WAY OUT OF THE USE OF THIS SOFTWARE, EVEN IF ADVISED OF THE POSSIBILITY OF SUCH DAMAGE.